Децентрализованный VPN и традиционный VPN: в чём разница?
Большинство VPN не могут обеспечить ту приватность, которую обещают. Вот что на самом деле меняет децентрализация и почему архитектура вашего VPN имеет значение

Поделиться
Большинство людей используют VPN, чтобы сохранять приватность в интернете. Проблема в том, что традиционные VPN построены на противоречии: чтобы скрыть вашу активность от интернета, вы передаёте её компании и доверяете ей не подглядывать.
Децентрализованные VPN (dVPN) используют другой подход. Вместо того чтобы направлять трафик через серверы, контролируемые одним провайдером, они используют независимо управляемые ноды. Это устраняет единую точку доверия, отказа и логирования, которая делает централизованные VPN лотереей в вопросах приватности.
NymVPN идёт ещё дальше. Сочетая децентрализованную маршрутизацию с шумогенерирующим микснетом, он защищает не только ваши данные, но и ваши метаданные — паттерны трафика, которые раскрывают, с кем, когда и как часто вы общаетесь.
Как работает традиционный VPN?
Традиционный VPN шифрует ваш интернет-трафик и направляет его через сервер, контролируемый провайдером. Это скрывает ваш IP-адрес от посещаемых вами сайтов, но никак не скрывает вашу активность от самого провайдера. Провайдер видит всё, и у вас нет независимого способа проверить их заявления о том, что они не ведут логи.
Традиционные VPN централизованы: одна компания владеет или арендует все свои серверы, контролирует весь код и единолично принимает все решения о приватности. Рынок также более консолидирован, чем кажется. Например, Kape Technologies владеет растущим списком VPN: ExpressVPN, CyberGhost, Private Internet Access. Пользователи, выбирающие приложения в магазине, могут думать, что это разные продукты, но на самом деле это просто активы одной и той же компании.
Чтобы использовать традиционный VPN, нужно верить, что:
- Провайдер не отслеживает вашу активность
- Провайдер не продаёт ваши данные третьим лицам
- У бизнеса и его инвесторов нет связей с правительствами или брокерами данных
- Кодовая база безопасна и постоянно поддерживается
Было много задокументированных случаев, когда VPN-провайдеры обещали политику отсутствия логов, а затем передавали данные пользователей под юридическим давлением. IPVanish, позиционировавший себя как сервис с «нулевым логированием», в 2016 году предоставил ФБР журналы подключений в реальном времени. PureVPN сотрудничал с федеральными властями в 2017 году, несмотря на свою гарантию отсутствия логов. A CSIRO study of 283 VPN apps found that 18% did not encrypt traffic and 38% injected malware or tracking code.1
В конечном счёте, доверие — это не механизм приватности. Архитектура — вот что. Так какова архитектура вашего VPN?
Что такое децентрализованный VPN?
Децентрализованный VPN (или dVPN) направляет зашифрованный трафик через независимо управляемые ноды, а не через серверы, контролируемые одной компанией. Ни одна отдельная нода, оператор или организация не могут видеть одновременно, откуда исходит трафик и куда он направляется. Приватность обеспечивается структурой сети, а не политикой компании.
Что такое децентрализованный VPN (dVPN): это VPN, в котором трафик идёт не через серверы одной компании, а через независимые друг от друга серверы. Децентрализация устраняет единую точку доверия, отказа и логирования, которая присуща централизованным VPN. Многие dVPN используют блокчейн-системы для вознаграждения операторов нод.
Многоступенчатая маршрутизация по умолчанию
Традиционные VPN направляют трафик через один сервер, то есть сервер видит всю вашу сессию. dVPN по умолчанию направляют трафик через несколько независимых нод, поэтому ни одна нода никогда не имеет полной картины. Быстрый режим NymVPN использует две ступени; анонимный режим использует пять.
Важно: что делает dVPN по-настоящему децентрализованным?
Чтобы VPN был по-настоящему децентрализованным, он должен соответствовать двум условиям:
- Он по умолчанию многоступенчатый, минимум с двумя независимыми серверами.
- Эти серверы не принадлежат и не контролируются одним и тем же лицом или организацией.
Поэтому если VPN-компания предлагает функцию вроде двойного VPN, использование двух серверов не означает, что вы остаётесь приватным, поскольку одна компания может видеть ваши данные на обоих серверах.
Отсутствие централизованного логирования
Поскольку ноды управляются независимо, ни один центральный орган не может собирать логи или быть принуждён кем-либо к их передаче. Серверы NymVPN управляются энтузиастами приватности по всему миру, которые получают вознаграждение в токенах $NYM за качественное обслуживание пользователей. Даже если оператор вредоносной ноды попробует логировать трафик, он увидит только маленький зашифрованный кусок, из которого невозможно ничего понять.
Исходный код открыт и доступен для проверки
Традиционные VPN могут использовать открытые протоколы, такие как WireGuard, но их общая кодовая база является закрытой. Пользователи должны доверять, что код безопасен и хорошо поддерживается, не имея возможности проверить это самостоятельно. dVPN, как правило, имеют открытый исходный код: любой может проверить, провести аудит и оспорить реализацию. Но на это нельзя полагаться — всегда проверяйте сами!
Код NymVPN находится в открытом доступе и прошёл независимую проверку безопасности.
Бездоверительное управление сетью
Традиционные VPN поддерживают централизованный каталог серверов: одна компания решает, что доступно, а пользователи не имеют информации о том, как и почему. Топология сети NymVPN управляется через блокчейн Nyx. Никто единолично не решает, какие ноды работают в сети. Операторы нод получают вознаграждения в токенах $NYM в зависимости от производительности, при этом сеть перенастраивается каждый час для поддержания надёжности всей системы.
Чем NymVPN превосходит другие dVPN?
Большинство децентрализованных VPN защищают содержимое вашего трафика. NymVPN также защищает ваши метаданные. Теперь, когда ИИ используется в системах слежки, это более важная проблема, которую необходимо решить.
Что такое метаданные?
Метаданные — это всё, кроме самого сообщения: с кем вы общались, когда, как долго и откуда. Не имеет значения, что ваши сообщения зашифрованы, если виден характер вашего общения. Источник журналиста может быть идентифицирован только по частоте контактов. Связи активиста можно отследить, даже не читая его сообщения. Спецслужбы и системы слежки на основе ИИ нацелены именно на метаданные, потому что они сохраняются даже при шифровании.
Микснет защищает от слежки с помощью ИИ
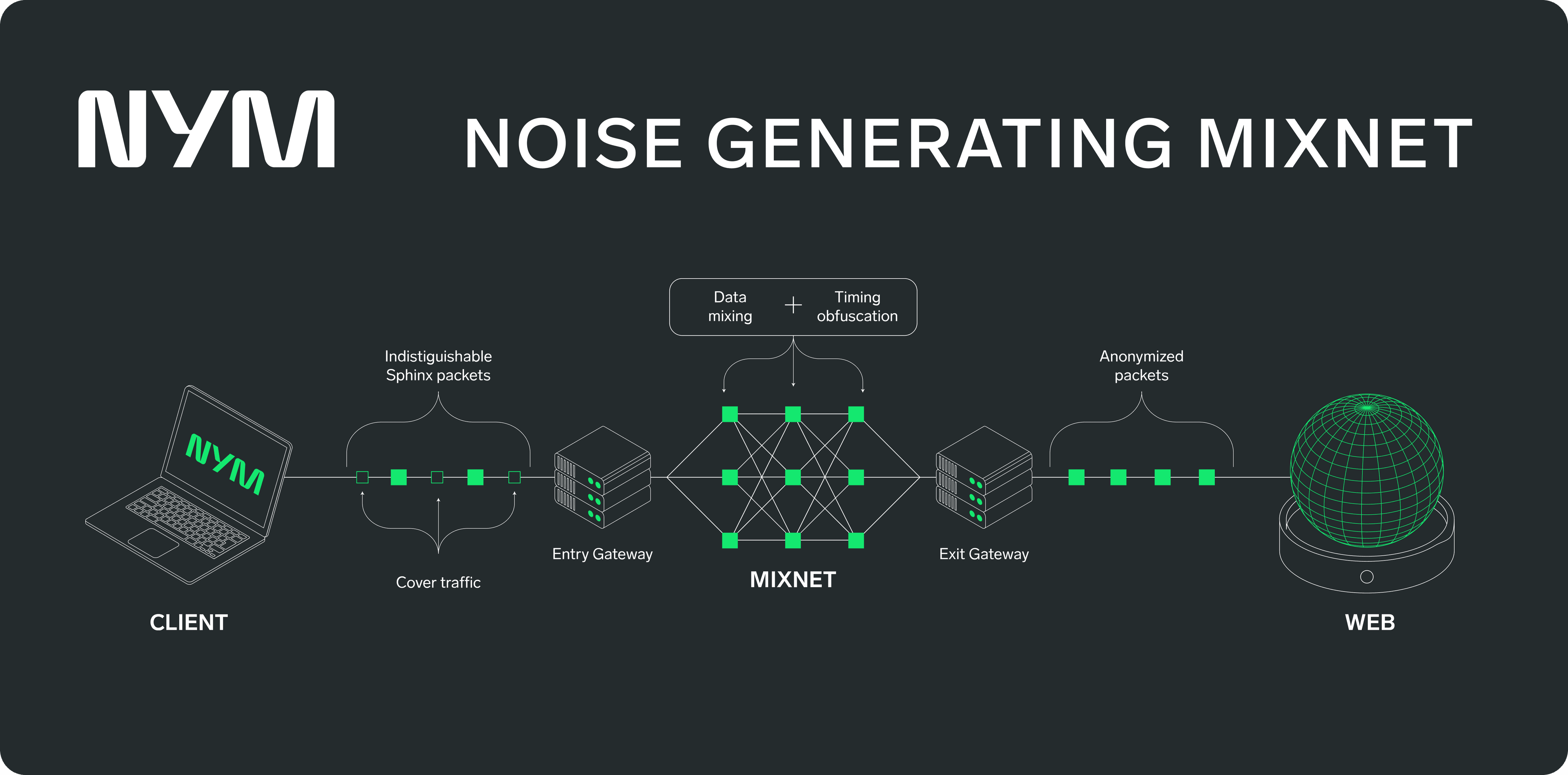
Анонимный режим NymVPN направляет трафик через 5-ступенчатый шумогенерирующий микснет: входной шлюз, три промежуточные миксноды, которые перемешивают и переупорядочивают зашифрованные пакеты, и выходной шлюз. Прикрывающий трафик добавляется для маскировки временных паттернов. Такая топология гарантирует, что ни одна отдельная нода не сможет связать пользователя с его трафиком, и даже ИИ будет крайне сложно с уверенностью восстановить ваш маршрут.
Микснет (mixnet) — это: сеть для приватности, где зашифрованные пакеты перемешиваются между множеством нод, а для борьбы с анализом трафика добавляется прикрывающий трафик. В отличие от простой многоступенчатой маршрутизации, микснеты меняют порядок пакетов и добавляют задержки — восстановить трафик становится вычислительно невозможно.
Не только приватность, но и скорость
Для пользователей, которые ставят скорость во главу угла, быстрый режим NymVPN обеспечивает двухступенчатую децентрализованную маршрутизацию через AmneziaWG — форк протокола WireGuard. Это гораздо приватнее любого традиционного VPN, а скорость соединения почти не уступает обычной.
Итак, нужен ли вам dVPN?
Традиционные VPN перекладывают проблему приватности, но не решают её. Вместо того чтобы доверять интернет-провайдеру, вы доверяете компании. Для журналистов, активистов и всех, кто живёт в условиях слежки — людей, для которых приватность не просто предпочтение, а необходимость, — это различие имеет огромное значение.
Децентрализованные VPN самой своей архитектурой устраняют единую точку доверия. NymVPN добавляет защиту метаданных, с которой не могут сравниться ни традиционные VPN, ни стандартные dVPN. Он создан не только для борьбы с текущими системами сбора данных, но и для будущего приватного интернета.
Ссылки
- [CSIRO, ICSI, UC Berkeley](https://www.icsi.berkeley.edu/icsi/news/2017/02/android-vp
dVPN и централизованные VPN: Часто задаваемые вопросы
dVPN направляет зашифрованный трафик через независимо управляемые ноды, а не через серверы одной компании. Ни одна отдельная нода не может видеть одновременно и источник, и место назначения, что по замыслу устраняет централизованное логирование.
Да. Традиционные VPN обеспечивают реальную защиту, но они требуют, чтобы вы доверили весь свой трафик одной компании. dVPN распределяет это доверие между множеством независимых нод, поэтому ни один оператор не может залогировать полную сессию. NymVPN добавляет защиту метаданных на уровне микснета поверх децентрализованной маршрутизации.
При правильно спроектированном dVPN ни одна отдельная организация не обладает достаточным объёмом информации для идентификации пользователя. Архитектура NymVPN обеспечивает работу с нулевым разглашением: даже Nym не может связать пользователя с его трафиком.
Оба используют многоступенчатую маршрутизацию через независимые ноды. Tor полагается на добровольческие ноды без экономического стимула, что влияет на надёжность. dVPN вознаграждают операторов через блокчейн-токены. NymVPN дополнительно обеспечивает прикрывающий трафик и временну́ю обфускацию, которых нет в Tor.
Многоступенчатая маршрутизация добавляет некоторую задержку. NymVPN стимулирует операторов за производительность, а пользователи выбирают уровень защиты: быстрый режим (двухступенчатая маршрутизация, оптимизированная для скорости) или анонимный режим (пятиступенчатый микснет для максимальной приватности).
Многоступенчатая маршрутизация увеличивает задержку по сравнению с прямым подключением, а качество нод в децентрализованной сети различается. dVPN также, как правило, имеют меньшее количество серверов, чем крупные централизованные провайдеры, что может повлиять на доступ к стриминговым сервисам. NymVPN решает проблему производительности с помощью токен-стимулов, которые вознаграждают надёжных операторов, и предоставляет пользователям выбор между скоростью (быстрый режим) и максимальной приватностью (анонимный режим).
dVPN устраняют централизованные хранилища данных, которые могут быть изъяты по запросу или захвачены. Микснет NymVPN идёт ещё дальше, делая паттерны трафика ненаблюдаемыми даже для сложных противников на сетевом уровне. Обратите внимание, что законность VPN варьируется в зависимости от страны, поэтому обязательно ознакомьтесь с местными правилами.
Об авторах

Casey Ford, PhD
Руководитель отдела коммуникацийСодержание
Продолжить чтение...

Nym - это больше, чем VPN
Первое приложение, которое защищает вас от слежки ИИ с помощью шумогенерирующего микснета
Пошаговое руководство по анонимному режиму
Как работает микснет Nym для защиты вашего трафика

Резкое снижение цен на NymVPN: как мы боремся за открытый интернет для всех
Делаем NymVPN доступным для людей по всему миру, чтобы бороться с цензурой и строить открытый и приватный интернет